posted: December 12, 2020
tl;dr: A primer on my favorite, convenient way to pass secrets, onetimesecret.com...
Email is insecure. I learned this lesson back in the 1980s while a student at Cornell. That was the first time I had an email account, on the pre-Web Internet. I was a student studying computer engineering and working in the Computer Science department, and I asked one of the smart people there how email worked.
That’s when I first learned about email relay servers, and how an email is basically a plaintext file that is transferred from server to server until it reaches a destination mail server. On any server, the file can be viewed by someone with system administrator privileges. Files can persist on servers, and copies can be made. Back then, there was no network-layer encryption, so the email’s contents could also be seen by someone who was “sniffing” (i.e. monitoring) the network traffic. A lightbulb clicked on in my head: an email can pretty easily be read by people other than the recipient, so I shouldn’t put highly confidential information in an email.
More than thirty years later, the U.S. presidential election of 2016 might have had a different result if one of the candidates had fully realized just how insecure email is.
Email is also discoverable, in a legal case. If you work for a company that gets sued, which happens all the time in larger companies, one of the first things that the lawyers for the plaintiff will do is depose all the company’s email communications during the timeframe in which the activities of interest took place. The plaintiff’s attorneys take this massive dump of archived emails and run it through search software looking for keywords of interest to their case. They are seeking “smoking gun” emails in which company personnel either plot or admit to having done actions that support the plaintiff’s case. So a given email may resurface years later in a court of law, and even end up being read on the national nightly news, if it is a big enough case and a damaging enough email. The lesson here is: do not put anything in an email that you wouldn’t want to be plastered all over television and the Internet.
According to news articles such as this one, the winning candidate in the U.S. presidential election of 2016 uses email only “very rarely”. This is actually a common practice among top business leaders, who prefer other, less discoverable, means of communication.
onetimesecret.com is an elegantly simple webapp to share secrets via a works-once URL
Although it lacks security, email is ubiquitous and easy to use. So occasionally people will use it to email me secrets such as passwords and account credentials. When that happens, I like to tell them about a secret passing tool that adds just one or two steps to the process of transferring a secret via email, and makes the secret transferring process much more secure. I learned about this tool in 2015 when a smart IT person told me about it, and have used it ever since. Hopefully this post will cause the tool to gain a few more users, and perhaps save some people from having their secrets compromised.
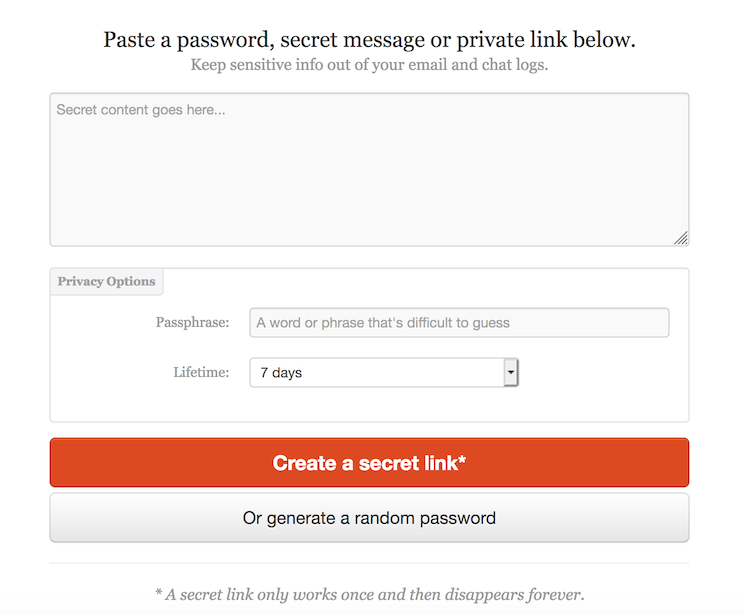
The tool is One-Time Secret. It is free and open source, and it is available at onetimesecret.com. When you click that link, you will be taken to a page that has a large text box in which you type, or copy-and-paste, the secret. For additional protection, you can enter a passphrase that is used to encrypt the secret while it is being stored on the server at onetimesecret.com. When you click on the “Create a secret link” button, a brand new unique URL will be generated. It is that URL that you copy and paste into your email to the recipient of the secret information. You are emailing a URL, not the secret itself, to the recipient. If you entered a passphrase, you can use a second form of communication, such as a text message, to send the passphrase to the recipient, for extra protection against interception.
The recipient receives your email, and possibly the passphrase. The recipient clicks on the URL, and possibly enters the passphrase. The recipient then sees the secret, which the recipient should now place in a secure location within the recipient’s IT infrastructure. The secret is delivered to the recipient’s web browser via HTTPS, so there is end-to-end encryption between onetimesecret.com and the recipient, just like there was end-to-end encryption between your browser and onetimesecret.com when you entered the secret.
The reason it is called “One-Time Secret” is because the URL only works one time to retrieve the secret. If the recipient, or a malicious actor, tries to click on the URL again, an error page is shown. If the recipient gets the error page the first time that the recipient clicks on the URL, the recipient knows that the secret has been compromised. Hopefully, the secret can quickly be changed and resent. The passphrase can help protect against this situation, because a malicious user would have to get access to both the email and the passphrase in order to retrieve the secret, and would have to do so before the recipient does.
One of the several ingenious aspects of onetimesecret.com is that you don’t have to trust onetimesecret.com in order to use it, if you use it properly. The folks at onetimesecret.com indeed might be able to see the secret, by looking within their server. But if you don’t put any text in the box that explains what the secret is for, they won’t know how to take advantage of having the secret. They will just see a new secret entered into their server by someone at some IP address on the Internet, and then retrieved later by someone else at some other IP address on the Internet. Unless the text in the secret box explains what the secret is for or how to use the secret, it will just be some meaningless (to onetimesecret.com) text. So put just the password (or other secret) into the secret box; don’t explain what the password is for. Your recipient should already know.
Is this system absolutely secure and unhackable? No computer system, with humans added into the mix, is. But I consider it to be good for most business IT uses, and far better than using plain email. I wouldn’t use it to transfer the launch codes for the U.S. nuclear weapons arsenal. If the computers running the browsers at either end are compromised such that they can capture the information in the browser and send it to a malicious actor, then the secret would be compromised, and probably also how to use it.
Kudos to the folks who built and maintain onetimesecret.com. The code is open source and available on GitHub, so it can be examined for security holes. That code can also be run on your own company’s server, if you really don’t trust onetimesecret.com at all, are worried about downtime, or want to add your own branding. There are also other copycat sites on the Internet running that same or similar code, such as cloak.sh. But you don’t have to run your own server unless you really want to. Just go to onetimesecret.com.