posted: May 22, 2021
tl;dr: A lesson I was taught as a child helps avoid several types of online scams...
One of the most important lessons my mother taught me as a child, which decades later I still apply daily in an Internet-connected world, was three simple words: “consider the source”.
She trotted out that saying when I or my siblings were upset about something that one of our peers had said. Kids can be all too mean at times. They like to tease, engage in one-upmanship, or simply enforce their definition of normality by denigrating someone who is a bit different. What my mother meant by the saying was that, before you react to the words that are being said, you need to assess who is saying them. Is that person someone who has earned the right to make those statements? Or is it someone whose words should be treated with no more respect, and perhaps less, than one’s own?
“Consider the source” has two major applications in today’s networked world, where psychology has become such an important aspect of the software we use: email phishing attacks and social media posts.
Email phishing attacks succeed not because they use sophisticated computer engineering, but because they use social engineering. Typically they trick recipients into thinking that the email is coming from a legitimate source by impersonating a trusted company or person. This is not too difficult to do: anyone can grab an image of the logo of a legitimate company, set up a burner email account and/or domain (perhaps purchased for less that $10 from namecheap.com), and send emails that appear to come from that company. Links in the phishing email take victims to a shady website set up by the scammer, which will often attempt to glean personal information from the victim or push a virus to their computer. The only real challenge the attackers face is the psychological one of tricking as many victims as possible to fall into the trap.
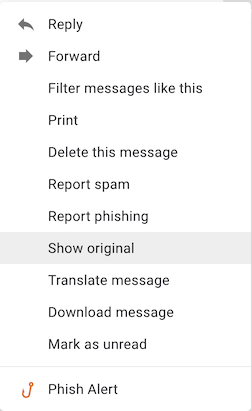
Gmail's command to view the source of an email: Show original
“Consider the source” is a good way to avoid becoming an email phishing attack victim. I do this as a matter of course, by checking who and where the email came from, i.e. the source, before acting upon it. The two web-based email clients that I use most often, Gmail and Outlook/Hotmail, each show the email address the email was sent from if you hover over the human-readable name in the “From:” field. I ask myself: does the domain seem legitimate? If the email claims to be from Amazon, is it sent from amazon.com or from amazonsomething.com? It is trivial to register a domain name that has some well-recognized domain name as part of it, or is a slight misspelling. Do the links in the email also go to legitimate, recognized domains when you hover over them?
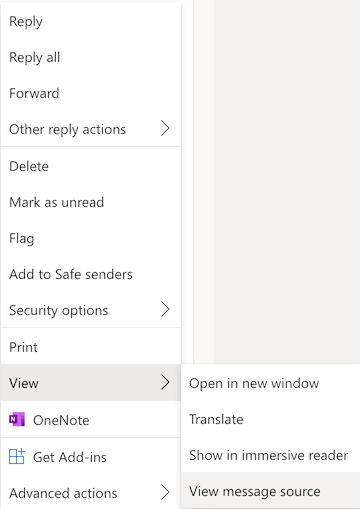
Outlook/Hotmail's command to view the source of an email: View > View message source
For the more technically adept, or curious, there is another way to “consider the source”: viewing the actual source code and text of the email itself. What you see when you look at an email with your email client is a clean, pretty, rendered image of that email. Behind, or one layer below, that rendered image is the actual source code of the email, which the email client interprets in order to display the rendered image. Both Gmail and Outlook/Hotmail provide a way to view the email source, on the pop up command menu which appears when viewing an email. On Gmail it is “Show original” and on Outlook/Hotmail it is “View > View message source”. At the top will be some dense text which shows a lot of technical details about the various network hops that the email took to reach you from the original sender, and below, typically, will be a bunch of HTML that constitutes the body of the email.
You may be surprised to see where many of the suspicious emails you’re receiving originate from. Often I will find emails that came from or traversed servers from countries notorious for Internet hacking, such as Russia.
To remind people of the need to exercise vigilance when going through their inboxes, my employer has been running a “white hat” phishing program. This program sends phishing attacks to employees at random, and measures whether someone clicked on a link in the email. The link doesn’t go to an actual shady site, but it does register the click indicating that someone fell for the phishing attack. To report a phishing attack, there is an additional “Phish Alert” command in the email popup menu in Gmail. We usually have phishing click-through rates that are well below industry average, and we recently had a month where not a single person clicked on a link in a white hat phishing attack. For any sizable group of people, it is hard to achieve perfection, as it does take some time, discipline, and the right mindset to recognize every single phishing attack. One tool that definitely helps is the lesson my mother taught me decades ago: “consider the source”.
Related post: Consider the source: social media